Journal article: Towards a categorization of scambaiting strategies
Title: Towards a categorization of scambaiting strategies
Author(s): Andreas Zingerle
Email: andreas.zingerle (at) ufg.ac.at
Published at: International Journal of Art, Communication and Design Technologies
The mission of the International Journal of Art, Culture and Design Technologies (IJACDT) is to promote an interdisciplinary research approach to understand cutting-edge theories and practices arising from the influence of technological innovation on creativity. IJACDT bridges the knowledge communication gap across humanities, scientific, and technical disciplines. IJACDT is at the epicenter of technological-scientific-artistic research and provides a common platform for information exchange between academia and industry, between scholarship and professionalism, between theory, criticism, and practice.
Abstract:
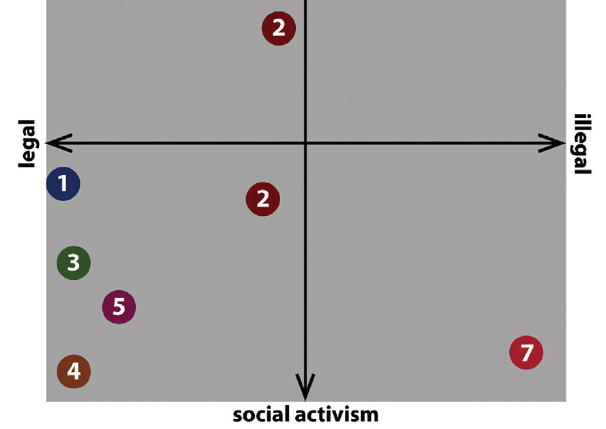
Scambaiters are individuals in online information communities specializing in identifying, documenting and reporting actions of so-called ’419 scammers’. A qualitative research approach was applied to two active scambaiting communities – 419eater.com and thescambaiter.com. Content analysis of several discussions and the examination of interviews from the web radio ’Area 419: Scambaiting Radio’ resulted in the seven categories of scambaiting techniques that are presented in this article. The aim is to both give a wider understanding of the scope of existing Internet scams as well as answering questions of why and how individuals or communities of scambaiters take action against Internet scammers. The analysis on various scambaiting practices is intended as a base for future discussions, for instance, whether some scambaiting methods should be implemented in media competence training.
Keywords:
Unsolicited electronic mail, Scambaiting, Computer mediated communication, Interactive storytelling.
References:
Berry, M. (2006). Greetings in Jesus Name. Harbour Books.
Bluth, B. (2010, Oct. 24). Area 419: Scambaiting Radio. Retrieved from http://itunes.apple.com/us/podcast/area-419-scambaiting-radio/id359035187
Brunton, F. (2013). Spam: a shadow history of the Internet.
Burrell, J. (2012). Invisible Users: Youth in the Internet Cafés of Urban Ghana. The MIT Press.
Cambaiter, W. S. (2012). Hello Sweaty. CreateSpace.
Espiner, T. (2007, Jan 17). Police maintain uneasy relations with cybervigilantes – CNET News. Retrieved Dec 18, 2013, from http://news.cnet.com/Police-maintain-uneasy-relations-with-cybervigilantes/2100-7348_3-6150817.html
Internet Complaint Center. (2013, May 14). IC3 Annual Report 2012. Retrieved Dec 18, 2013, from http://www.ic3.gov/media/annualreport/2012_IC3Report.pdf
Messaging Anti-Abuse Working Group. (2011). Retrieved Dec 18, 2013, from http://www.maawg.org/
Renner, K. N., Hoff, D., & Krings, M. (Eds.). (2013). Medien. Erzählen. Gesellschaft.: Transmediales Erzählen im Zeitalter der Medienkonvergenz (Vol. 2). Walter de Gruyter.
The Road to Chad/Darfur. (2010). Retrieved Dec 18, 2013, from http://www.419eater.com/html/RoadToChadDarfur/
Tuovinen, L., Röning, J., Tuovinen, L., & Röning, J. (2007). Baits and beatings: vigilante justice in virtual communities. In Proceedings of CEPE 2007. The 7th International Conference of Computer Ethics: Philosophical Enquiry (pp. 397–405).
Zingerle, A., & Kronman, L. (2011). Transmedia Storytelling and Online Representations-Issues of Trust on the Internet. In Cyberworlds (CW), 2011 International Conference on (pp. 144-151). IEEE.
Zingerle, A., & Kronman, L. (2013). 419fiction – anti-fraud activism. Retrieved Dec 18, 2013, from http://419fiction.kairus.org/