Artwork: Panopticity:Seoul
Title: Panopticity:Seoul
Type: Video
Production year: 2018
Running time: 6:00min
by KairUs Art+Research (Linda Kronman, Andreas Zingerle)
Location: Seoul, Republic of Korea
Voices:
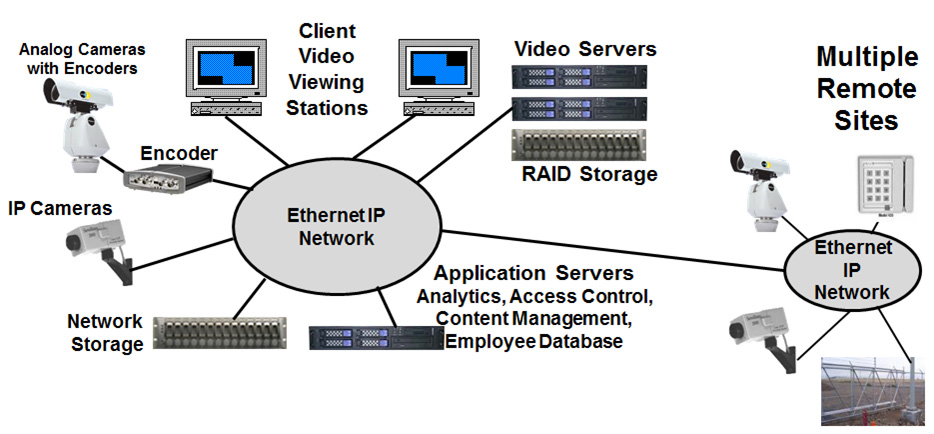
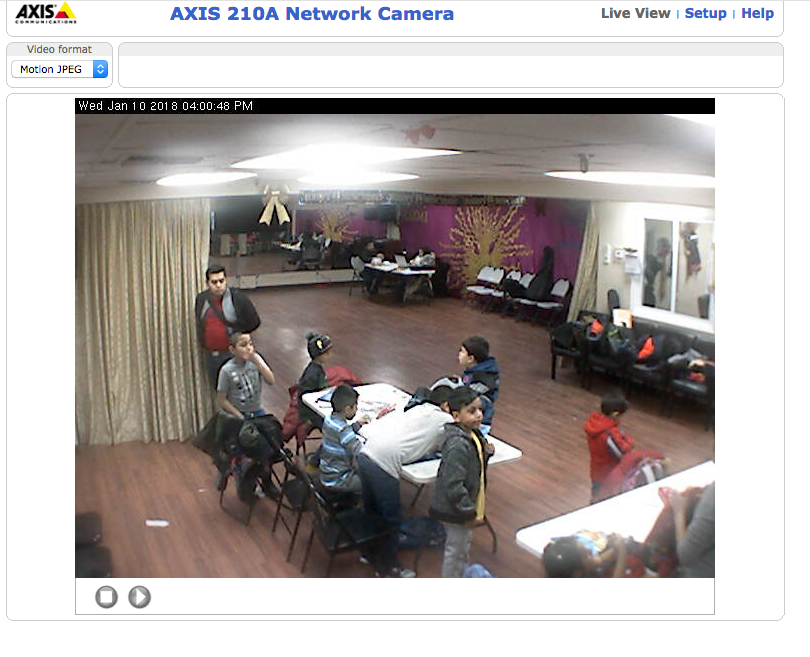
The video portrays the city of Seoul (South Korea), through the lenses of unsecured public CCTV and private IP cameras. Networked security cameras offer 24/7 surveillance. Tracking software and the integrated web-server allow processing and streaming as part of the growing amount of connected devices also known as the Internet of Things. These web-servers are often insecure by design, meaning they are not protected by a password or have hard-coded login credentials saved as plain text. By default, the servers stream unencrypted and on publicly-accessible network ports, providing potential risks of being intercepted and allowing unknown third parties unintended access to the set up function of the cameras. Some manufacturers use the same vulnerable settings across their entire camera lineup. “By default, the Network Camera is not password-protected”, or “the default user name is admin” and “the password is 12345” can be read in the camera manuals. Security cameras are supposed to offer security, not provide surveillance footage for anyone to view. Often, camera owners don’t realize that their cameras are accessible on the Internet with default insecure settings, enabling hackers to enslave these cameras into botnets. Malware will use insecure webcams to infect the rest of the network, routers and other devices in the “smart home”, threatening both the reliability of surveillance cameras and also serving as a transmission vector to attack other devices.
Link to the video (Password needed!):
Un-secure surveillance cameras:

Stills taken from the video:


Web-interface of surveillance cameras:
How does an attacker run DDoS attacks on a victim’s IP camera: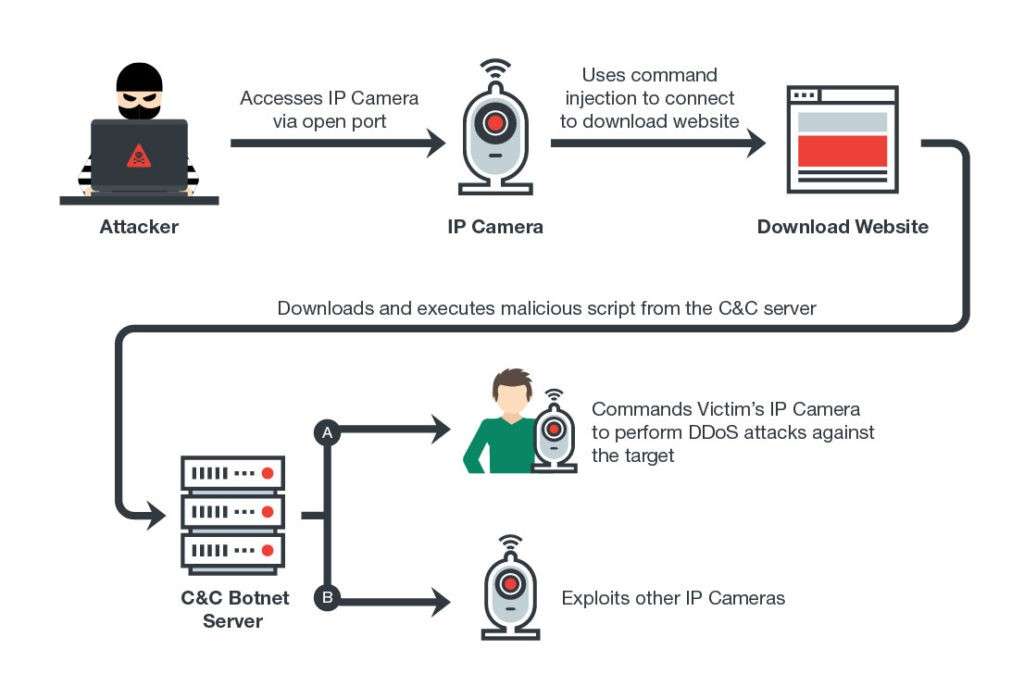
Screenings:
2018:
‣ Aksioma – Institute for Contemporary Arts, Ljubljana/Slovenia.
‣ Drugo-More, Rijeka/Croatia.